Fraud protection.
Now it's personal.
ANZ Falcon® technology monitors millions of transactions every day to help keep you safe from fraud.
Falcon® is a registered trademark of Fair Issac Corporation.
Stay informed on the latest scams, fraud, and security alerts. Learn about emerging cyber threats and important online risks as they arise. If you are a business, make sure to stay updated with the latest business security alerts that could impact you.
Explore the latest alerts below, and make informed decisions to help keep your personal and banking details safe.

![]()
Businesses: See latest security alerts
![]()

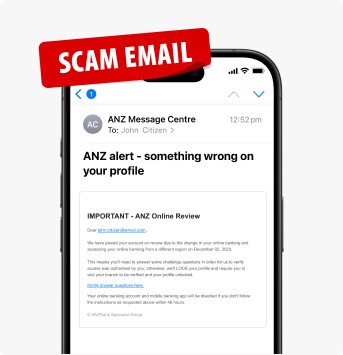
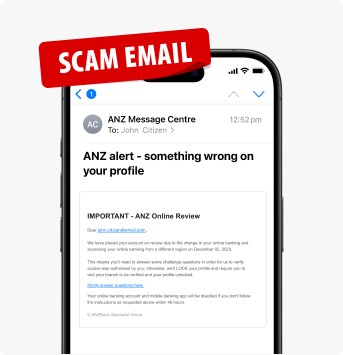
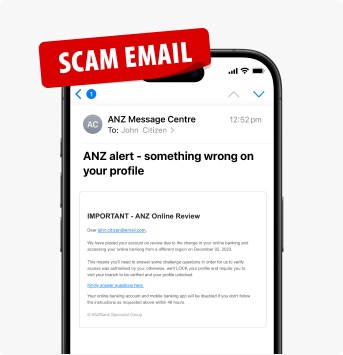
Posted on 15 May 2026
Type:
Be cautious of unexpected calls, messages or emails claiming to be from ANZ.
If something feels off - don’t respond, hang up and contact us using the number on our official website.
If you receive any suspicious emails or messages claiming to be from ANZ, please forward them to hoax@cybersecurity.anz.com.
Remember, we will never ask you to:
Posted on 20 February 2026
Type:
A scam has been identified where individuals are receiving calls from scammers pretending to be ANZ and then sending an “Advisor Verification” email to make the interaction look legitimate. This email may include a fake “verification code” that the scammer asks the recipient to read back - a tactic intended to create the impression that they are genuinely dealing with ANZ.
Engaging with the scammer may result in unauthorised transfers or account misuse.
Always be wary of unexpected calls, messages or emails claiming to be from ANZ. If something feels off, hang up and contact us using the number on our official website.
If you receive any suspicious emails claiming to be from ANZ, please forward them to hoax@cybersecurity.anz.com.
ANZ will never ask you to:
Type:
A scam has been identified where individuals are receiving emails impersonating ANZ claiming that a new direct debit has been set up. These emails may reference the name of a legitimate business and urge the recipient to call a mobile number if they did not authorise the direct debit.
Be cautious of unexpected emails, texts and calls claiming to be from ANZ.
ANZ will never ask you to:

Type:
We’re aware of sophisticated investment scams that use convincing tactics to steal your money.
These scams often start with social media ads that look legitimate and may even appear to be endorsed by trusted public figures. Once you engage, the scammer may present what seems like a great opportunity to grow your money, promising high returns in a short period of time. They may even encourage you to open new bank accounts, withdraw your savings/super into these accounts, and transfer the funds into a fake investment account they control.
Over time, you may try to withdraw your money only to find that your “account manager” stops responding or the investment platform suddenly becomes unavailable. By this stage, the scammers have taken your funds and disappeared.
Keep an eye out for these red flags:
![]()

Posted on 29 January 2026
Type:
During humanitarian crises or natural disasters, scammers may impersonate legitimate charities to trick people into donating to causes that are fake or misrepresented.
Scammers commonly use the following tactics to ask for fake donations:

Posted on 06 January 2026
Type:
A scam has been identified where individuals are receiving SMS messages impersonating ANZ Rewards. These messages may claim that rewards points are about to expire and include a link to redeem them.
Be cautious of SMS messages, emails or phone calls, claiming to be from ANZ. They may ask you to log in to your account through a link, provide sensitive banking details, download software, transfer money or open another account.
Remember, we will never ask you to:
![]()

Posted on 09 December 2025
Type:
From 10 December 2025, some social media platforms will be restricted, by law, to people aged 16 and over.
These laws require affected platforms to take reasonable steps to prevent anyone under 16 from creating or holding accounts.
These measures are designed to protect young people from the risks and pressures associated with social media use.
The National Anti-Scam Centre has warned about four potential scams that opportunistic criminals may use to take advantage of these changes:
![]()
Posted on 27 November 2025
Type:
Scammers are sending extremely convincing fake emails pretending to be from Services Australia and Centrelink. These scams have already hit over 270,000 inboxes nationwide targeting a wide range of organisations including schools, hospitals, law firms, corporations, and even government agencies.
The emails look real and often mention various Australian benefit systems like Superannuation or Family Tax Benefits. These emails are mostly written and sent using various techniques to avoid security or spam filters.
They deceive people into clicking links and entering personal details, which can lead to identity theft, account compromise, or even ransomware attacks.

Posted on 13 November 2025
Type:
A scam has been identified where individuals are receiving SMS messages impersonating ANZ Rewards. These messages may claim that rewards points are about to expire and include a link to redeem them.
Be cautious of SMS messages, emails or phone calls, claiming to be from ANZ. They may ask you to log in to your account through a link, provide sensitive banking details, download software, transfer money or open another account.
Remember, we will never ask you to:
![]()

Posted on 05 May 2026
Type:
The ASD's ACSC has published a critical alert regarding a critical vulnerability (CVE-2026-4194) affecting cPanel/WHM products.
The vulnerability is an authentication bypass, which can allow unauthenticated remote attackers to gain access to the control panel, as well as conduct remote code execution (RCE).
The vulnerability affects all versions after 11.40 (which was released in 2013).
Patches have been released as of 30 April 2026.
ASD’s ACSC does not have information to indicate that a specific industry or sector is being targeted.

Posted on 28 April 2026
Type:
ASD’s ACSC is aware of new information on a previously unknown persistence mechanism that is preserved across even when upgrading on Cisco Firepower and Secure Firewall products running ASA or FTD software.
CISA and NCSC have identified new malware deployed as part of the historical exploitation of CVE-2025-20333 and CVE-2025-20362, affecting devices running Cisco Secure ASA Software or Cisco Secure FTD Software. Australian organisations can find details on this FIRESTARTER malware.
This malware can persist as an active threat on Cisco devices running ASA or Firepower Threat Defense (FTD) software, maintaining post-patching persistence and enabling threat actors to re-access compromised devices without re-exploiting vulnerabilities.
The following devices are in scope of this new malware:

Posted on 28 April 2026
Type:
The Australian Signals Directorate’s Australian Cyber Security Centre (ASD’s ACSC) is encouraging organisations to understand and take action on their cyber supply chain risk.
Cyber supply chain risk refers to vulnerabilities introduced by any third party that touches your products or services, meaning weaknesses can emerge at any point. From suppliers and manufacturers to distributors, retailers or contractors, each of these partners handles systems, components or data you rely on. Any compromise in their environment can directly become a compromise in yours.
Cyber supply chain risk management should form a significant component of any organisation’s overall cyber security strategy, and you must treat the security of your cyber supply chain as seriously as your own.

Posted on 02 April 2026
Type:
The ASD's ACSC has published a high alert regarding increase targeting of online code repositories, essentially the codes that run their website and systems.
Threat actors have been observed gaining access to online code repositories through:
The following activities have been noted as being performed by threat actors after gaining access to privileged systems and accounts:
Threat actors have been observed abusing legitimate tooling and functions to achieve these results, rather than bespoke tooling.
The risk of exposed code bases can give threat actors a better understanding of internal processes and systems, increasing an organisation’s exposure to attacks.

Posted on 02 March 2026
Type:
The ASD’s ACSC has issued a critical alert warning that malicious cyber threat actors are targeting organisations’ SD‑WANs globally.
These actors have exploited a Cisco Catalyst SD-WAN controller authentication bypass vulnerability, CVE-2026-20127.
After exploitation of this vulnerability, the malicious actors add a rogue peer, and eventually gain root access to establish long-term persistence in SD-WANs.

Posted on 06 January 2026
Type:
The ASD's ACSC has sent a critical alert relevant to Australian organisations and technical IT support service using WatchGuard Firebox.
An Out-of-Bounds Write vulnerability (CVE-2025-14733) enables an attacker to achieve unauthenticated Remote Code Execution (RCE) in the following vulnerable versions of the Fireware OS:

Posted on 11 December 2025
Type:
The ASD's ACSC has published a critical alert regarding multiple critical vulnerabilities in a number of Fortinet Products:

Posted on 05 December 2025
Type:
The ASD's ACSC has published a critical alert regarding vulnerabilities affecting React Server Components, which is used extensively in modern web applications.
According to the ASD’s ACSC, the vulnerability (CVE-2025-55182) enables an attacker to achieve unauthenticated Remote Code Execution (RCE) in vulnerable versions of the following packages:

Posted on 06 November 2025
Type:
ASD’s ACSC has identified corporate network breaches that started in employees accessing work resources or systems from personal devices infected with malware called information stealers.
Info stealers, are a type of malware designed to collect information from a victim’s device.
Organisations that allow employees, contractors, managed service providers or other entities to access their network remotely, including with Bring Your Own Device (BYOD) hardware, need to be aware of the risks and protect themselves from this threat.

Type:
The ASD's ACSC has published a critical alert regarding the following vulnerability in the Microsoft Windows Server Update Service:
The vulnerability impacts Microsoft Windows Server Update Service in Windows Server (2012, 2016, 2019, 2022 and 2025).

Posted on 17 October 2025
Type:
The ASD's ACSC has published a critical alert regarding multiple high-severity vulnerabilities in F5 products and an incident impacting F5.
According to the ASD’s ACSC, F5 have released an advisory regarding a cyber security incident that has affected certain F5 systems with recommendation on what customers can do to help protect themselves.
In addition to this advisory, F5 has issued its October 2025 quarterly security notification summarising multiple critical vulnerabilities identified across its product portfolio.
![]()
App Store is a service mark of Apple Inc. Google Play and the Google Play logo are trademarks of Google LLC